The Economics of Smart Contract Exploits
Every smart contract exploit is, at its core, an economic transaction. Attackers invest resources (time, capital, risk) in exchange for potential profit. Understanding this economics is crucial for building secure protocols.
The Attacker's Calculus
Before launching an exploit, sophisticated attackers evaluate:
Expected Value
E(attack) = P(success) × Profit - P(failure) × Loss - Opportunity_Cost
Where:
- P(success) - Probability the exploit works
- Profit - Value extracted if successful
- P(failure) - Probability of detection/prevention
- Loss - Costs if attack fails (gas, seized funds)
- Opportunity_Cost - What else they could do with their capital
Attack Costs
Modern exploits aren't free. Attackers must pay for:
| Cost Category | Typical Range |
|---|---|
| Vulnerability Research | 10-1000 hours |
| Exploit Development | 5-100 hours |
| Flash Loan Fees | 0.05-0.3% of borrowed |
| Gas Costs | $100-$10,000 |
| Capital at Risk | Variable |
Why TVL Matters
Total Value Locked (TVL) is the primary driver of attack incentives. The relationship is exponential:
- $1M TVL: Hobbyist attackers, low sophistication
- $10M TVL: Professional attention, some resources invested
- $100M TVL: Serious operators, significant investment justified
- $1B+ TVL: Nation-state level attention, unlimited resources
This is why protocols often face more attacks as they grow—the economics increasingly favor exploitation.
The Security Investment Equation
For protocol teams, security is also an economic decision:
Cost of a Hack
Beyond the direct loss of funds, exploits cause:
| Impact | Estimated Cost |
|---|---|
| Direct fund loss | 100% of exploited value |
| Token price crash | 30-80% of market cap |
| User trust erosion | Hard to quantify |
| Legal/regulatory exposure | $100K-$10M+ |
| Recovery efforts | Months of team time |
The total cost typically exceeds the direct loss by 2-5x.
Cost of Security
Compare this to security investment:
| Security Measure | Typical Cost |
|---|---|
| Traditional audit | $50K-$500K |
| AI-powered audit | $5K-$50K |
| Bug bounty program | Ongoing % of TVL |
| Formal verification | $100K-$1M |
The math is clear: a single prevented exploit pays for decades of security investment.
Risk-Based Security Strategy
Smart protocols match security investment to risk:
Tier 1: Critical Path
Functions that handle money directly:
- Withdraw/transfer operations
- Price oracle integrations
- Liquidation mechanisms
Security approach: Maximum coverage, formal verification, multiple audits
Tier 2: Admin Functions
Governance and configuration:
- Parameter updates
- Access control changes
- Upgrade mechanisms
Security approach: Time locks, multi-sig, careful audit
Tier 3: View Functions
Read-only operations:
- Balance queries
- State inspection
- Helper functions
Security approach: Standard review, lower priority
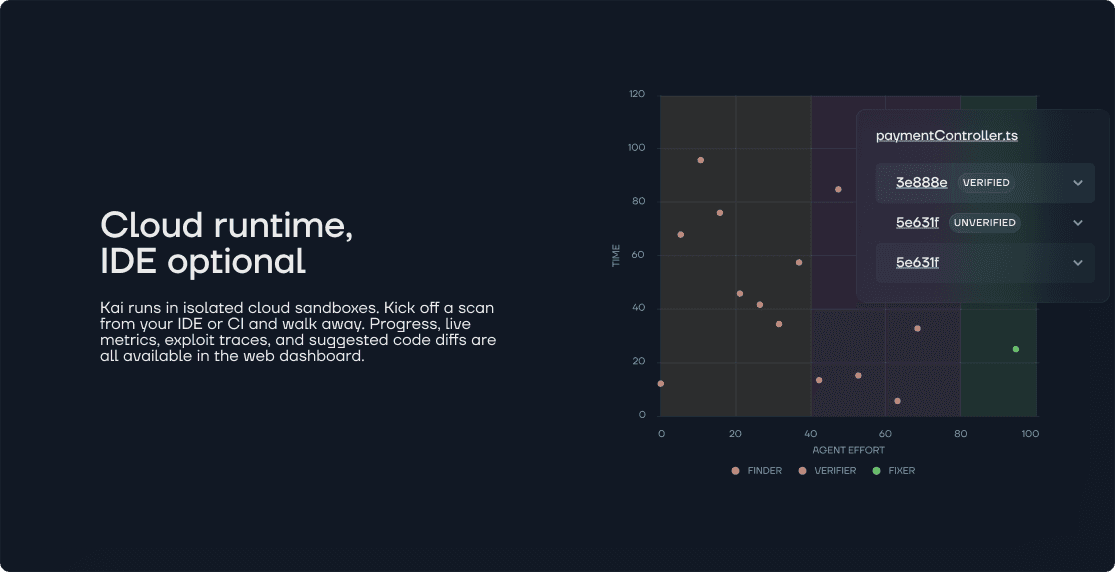
The AI Advantage
AI-powered security shifts the economics in favor of defenders:
Traditional Economics
Attacker: 100 hours research → finds 1 vulnerability
Defender: 100 hours audit → reviews 10% of code
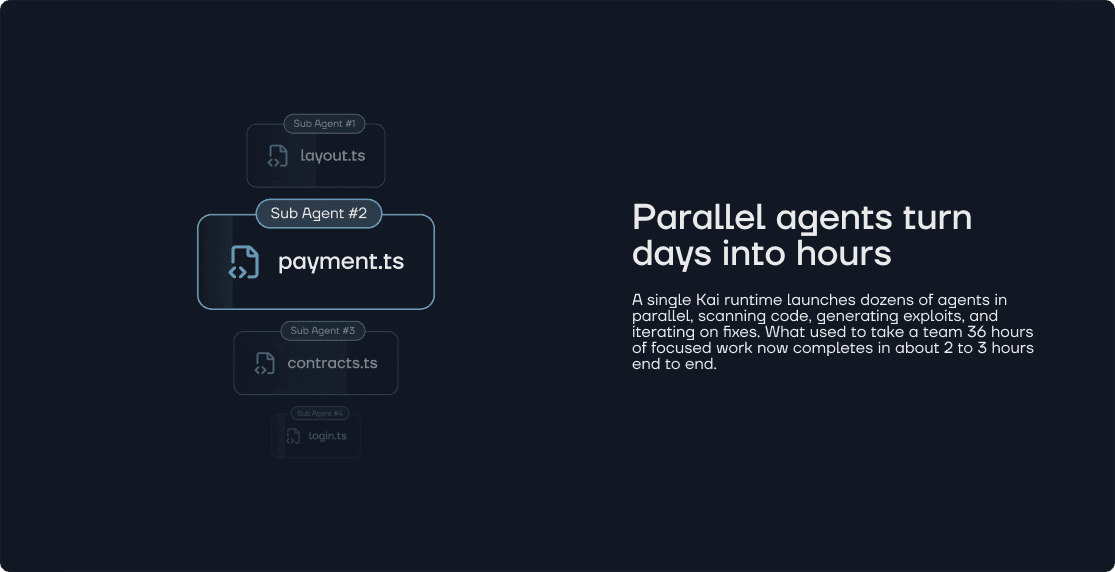
AI-Augmented Economics
Defender: 1 hour AI scan → reviews 100% of code
Defender: 10 hours triage → verifies all findings
Result: Attacker's research becomes worthless
By dramatically reducing the cost of comprehensive coverage, AI makes security economically viable even for smaller protocols.
Recommendations
Based on our analysis:
- Security budget = 1-5% of TVL annually - This provides appropriate coverage
- Continuous monitoring > point-in-time audits - Attacks don't wait for audit schedules
- Layered defense - Combine multiple approaches (audits, monitoring, insurance)
- Economic deterrence - Bug bounties that match exploit potential
The protocols that survive long-term are those that make attacks economically irrational.
Calculate your protocol's risk profile with Kai.