Understanding Invariant-Based Vulnerability Detection
When we talk about finding vulnerabilities in smart contracts, most people think of common patterns: reentrancy, overflow, access control. But the most devastating exploits often violate something more fundamental—invariants.
What Are Security Invariants?
An invariant is a property that must always hold true, regardless of what operations are performed. Think of them as the laws of physics for your protocol:
// Example invariant: Total deposits should always equal
// the sum of all user balances
assert(totalDeposits == sumOfAllBalances);
When an invariant is violated, something has gone fundamentally wrong. Money has been created from nothing, or permissions have been bypassed, or state has become inconsistent.
Categories of Invariants
Through our research, we've identified several categories of invariants that appear across protocols:
1. Conservation Invariants
These ensure that value is neither created nor destroyed unexpectedly:
- Total supply of tokens remains constant (unless minting/burning)
- Sum of balances equals total locked value
- Fees collected equal fees expected
2. Access Control Invariants
These protect privileged operations:
- Only designated roles can execute sensitive functions
- Ownership cannot be transferred to zero address
- Time locks are respected
3. State Machine Invariants
These ensure the protocol moves through valid states:
- A loan cannot be liquidated before it's undercollateralized
- An auction cannot be settled before it ends
- A proposal cannot be executed before voting concludes
4. Arithmetic Invariants
These prevent numerical errors:
- No operation should cause overflow/underflow
- Division by zero is impossible
- Precision loss is bounded
Why Automated Discovery Matters
Here's the critical insight: developers often know their invariants implicitly but never formalize them. This creates a gap where:
- Auditors must deduce invariants from code and docs
- Deductions may be incomplete or incorrect
- Violations of unstated invariants go undetected
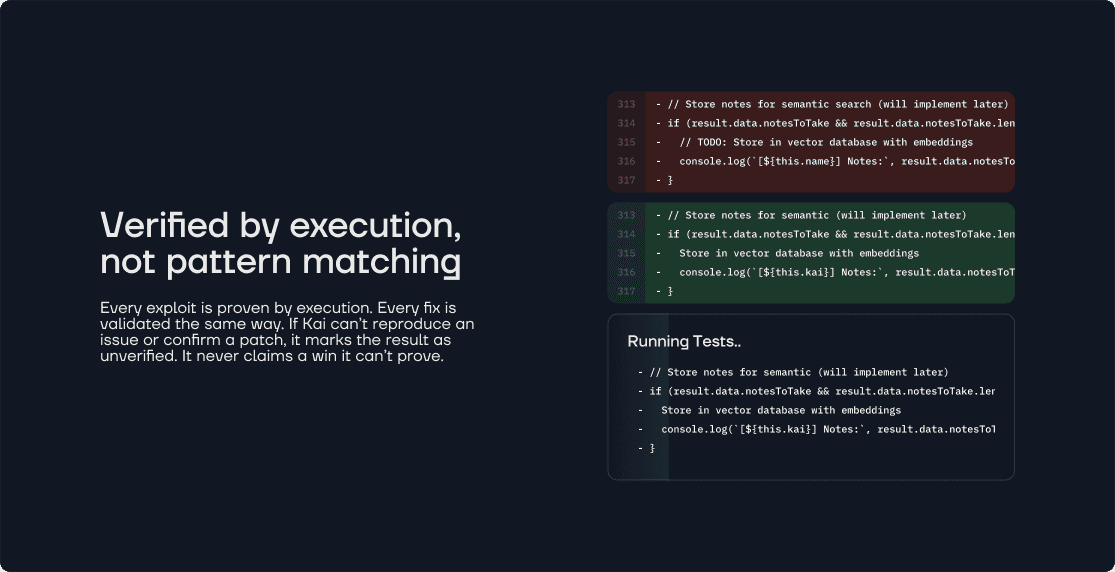
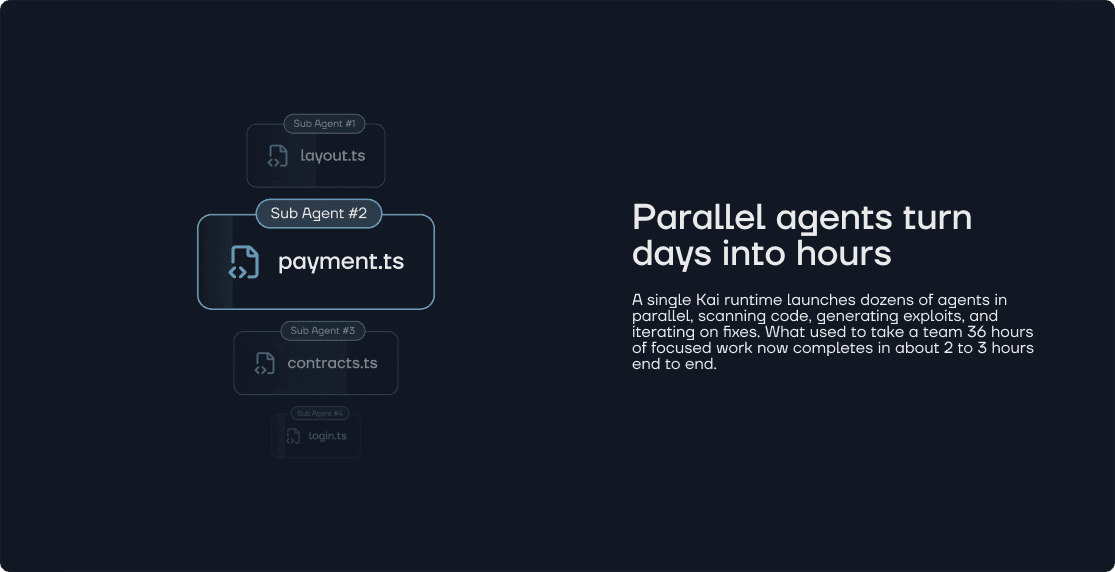
AI-powered tools like Kai bridge this gap by:
- Analyzing code patterns to infer likely invariants
- Generating formal specifications automatically
- Testing those invariants against all possible execution paths
Case Study: The Stale Confirmations Bug
In our recent audit of a MultiSig Timelock contract, we discovered an invariant violation that manual review missed:
Expected Invariant: txn.confirmations should always reflect confirmations from currently valid signers.
Actual Behavior: Confirmations persisted even after signers were revoked.
This subtle violation meant that transactions could be executed with "stale" approvals from users who were no longer authorized. The invariant-based approach revealed what pattern matching never would.
Building Invariant Awareness
For protocol developers, we recommend:
- Document your invariants explicitly - Write them down, even if they seem obvious
- Test invariants in your test suite - Use assertion-based testing
- Consider formal verification - For critical protocols, prove invariants mathematically
- Use AI-powered auditing - Let machines find what humans miss
The future of smart contract security isn't about finding more bugs—it's about proving properties hold. Invariants are the foundation of that future.
Want to discover the invariants in your protocol? Try Kai for AI-powered invariant detection.